 This is a corrected version of what I posted 4 months ago in this forum here.
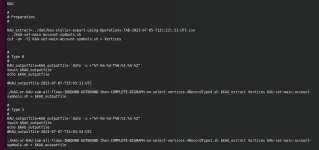
This is a corrected version of what I posted 4 months ago in this forum here.In the next post, I'll show what I ran to produce this result.
bash cource code is at github
here
and
here
All based on previous work I have documented on this forum over the last few weeks in particular.
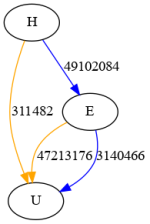
I use the same bash script to work on KAG and KAU.
The subtlety is in the parameters you pass to the script files.
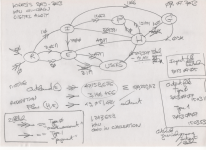
See photograph in next post (...).
The 2 output files as well. At github.
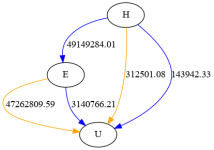
Please read the pic, bottom right to see exactly which output files I use to draw to draw the digraph enclosed.